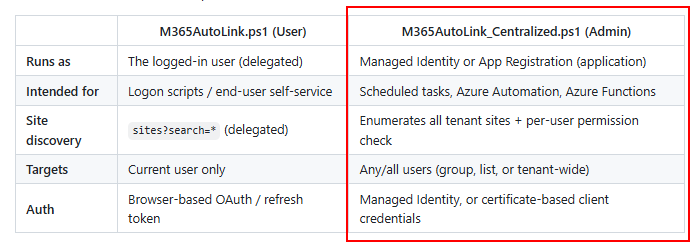
Doing logon scripts is easy for some, less easy for others, and in general not great in certain types of environments.
And this led to some questions if I could also make a version of M365AutoLink that can run centrally. There was a hurdle to overcome: how do we know what libraries a user has access to?
M365Permissions already has the answer, so a quick copy paste from the code there and voila, we now have a centrally runnable version of M365AutoLink!
It can run either as managed identity, or cert-based service principal. I recommend running it as a runbook, and don’t run it on tenants with thousands of users or commercially….for commercial use click here 🙂
For full documentation and code: https://github.com/jflieben/M365AutoLink